Guest
Guest
Create New Topic As guest or Sign in
Assign topic to the user

-
TISAX and ISO 27001
I hope this message finds you well. We are in plan to implement TISAX and ISO 27001. we have one IT staff member and there is a confusion on whether he should be sitting by himself in a secure office/area. My CEO requested to ask if the clauses or interpretations in either TISAX or 27001 specifically call for IT staff to have their own office area. Our Current IT staff is sharing the office with a member from purchasing department.
-
Security Awareness Training Records
Is it compulsory to record attendance at this training? Would an ISO 27001 auditor require such a record?
-
Clarification Regarding Control Review Frequency in Policy Documents
I wanted to clarify that all the policy documents we've prepared specify a requirement for a 6-month review. However, the specific controls we discussed are not mentioned in the documents. My question is whether, according to the policy, we need to review the controls every 6 months or if we have the flexibility to define the update frequency for the controls ourselves, separate from the document reviews. Please refer to the attached image for more details.
-
Risk levels and decision-makers
About risk levels and decision-makers, could you share some insights? I got confused on who will be the decision maker on putting the level of the risk and based on which criteria the level was set?
-
ISO 27001 Internal Auditor Course Question
In Module 7 Audit Findings, the quiz asks to the student to select which finding is an observation with the correct answer nominated as “The procedure for internal audit can be improved by adding an audit plan”. I would argue that this is a non-conformity as ISO27001-2022 cl 9.2.2 requires the organisation to plan, establish, implement and maintain an audit programme(s), including the frequency, methods, responsibilities, planning requirements and reporting. If an audit plan is not available at the time of the audit, is this an matter of noncompliance with the part of the standard?
I’d appreciate your thoughts and any clarification that you might be able to provide.
-
Certification scope
As we have two entities, one in Site A operating under the supervision of the regulator and 2nd in Site B providing services for the Site A entity, a few things to clarify:
- Is the setup, documents, actions etc. enough for both entities, or I will have to prepare two different setups?
- Also do we have to pass an audit to certify both entities or only the regulated body is enough?
In addition to that, the situation now is slightly changed as we have another regulated entity in Site C and I need this to be added in the answer. I need clarification on how to action as we have now in total 3 companies under Company:
Company A - the Site B company that is providing services for the rest of the companies
Company B - the Site A-regulated company
Company C - the Site C-regulated company
-
Security Awareness Course Password Question
One of your questions/answers (
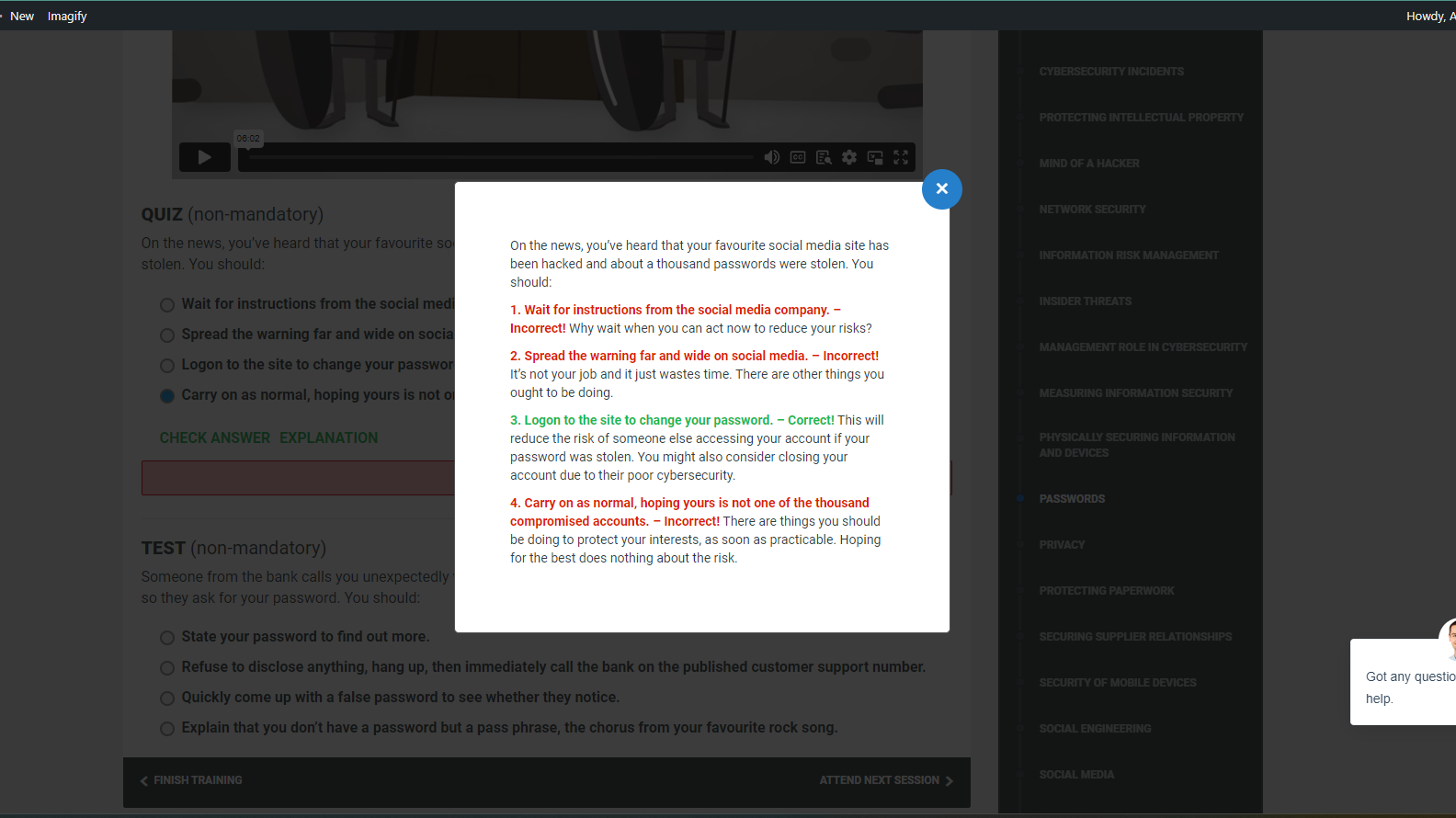 ) is incorrect according to typical security best practices. If the security of a website has been compromised, you should absolutely not long in immediately if they have not told you to. While you might consider changing passwords on any other site where you've used the same one, logging in and updating it on a site that may still have an incident in progress only increases your risk."
) is incorrect according to typical security best practices. If the security of a website has been compromised, you should absolutely not long in immediately if they have not told you to. While you might consider changing passwords on any other site where you've used the same one, logging in and updating it on a site that may still have an incident in progress only increases your risk." -
Change management and Change classification
How do we define what changes need to be regulated by the Change Management and what changes do not?
Can you maybe share a list with examples or criteria you see used?
-
Audit Questions
We recently had a client undergo a pre-assessment audit for their certification. During the audit, a couple of issues were raised:
The internal audit wasn't conducted properly due to insufficient time allocated for the process and the management system.
The auditors were seeking procedural documents that directly correlate with the Annex A policies provided in your templates.
Given these challenges, I wanted to reach out and seek your guidance. Specifically:Do you have best practices or guidance on how to ensure our internal audits are thorough and in compliance with the standards?
Are there any templates or resources available that can help us align our procedural documents with the Annex A policies you've provided? This would be incredibly helpful in ensuring our documentation meets the auditor's requirements.Furthermore, I'm curious if you have any templates or resources specifically for ISMS procedureal documents. We want to ensure that our ISMS documentation is both comprehensive and in line with industry standards.
-
Conformio questions
We just have a question regarding the documents and then we are happy to upgrade.
I generated Information Security Policy using the document wizard, but it was missing the following information:
- Exception Handling: How exceptions to the policy will be managed is not stated. Usually, there's a process for requesting an exception and how it's reviewed.
- Consequences of Non-Compliance: Outline what the consequences are for employees who do not adhere to the policies.
- Links to Other Policies and Procedures: Usually, the top-level policy should link to or reference other detailed policies and procedures (e.g., Access Control Policy, Incident Response Plan).
- External Parties: You mention that the policy applies to 'relevant external parties'. It might be useful to specify who these external parties are (vendors, contractors, etc.).
- Review Frequency: You've stated the document must be reviewed every 12 months. It's good to also mention under what other conditions a review would be triggered (e.g., after a security incident).
- Audit and Monitoring: There's no mention of how compliance with this policy will be audited or monitored.
- Document Storage and Versioning: Information on where this document will be stored, how it will be versioned, and who will have access should be added.
- Terminology: While you've defined basic security terminologies, the inclusion of more specific terms used in the document might be beneficial.
Is there something we missed during the document wizard or anyway to generate the complete document?
Since we need to provide these policies to our customers and want to pass ISO 27001, that would be great to know how to generate the complete document.
